Introduction
Landing a ServiceNow ITOM role can transform your IT career, but the interview process can feel overwhelming. Whether you’re a beginner exploring IT Operations Management or an experienced professional looking to advance, having the right preparation makes all the difference.
This comprehensive guide presents 50 carefully curated ServiceNow ITOM interview questions and answers that hiring managers actually ask. We’ve researched real interview experiences, consulted with industry experts, and distilled complex concepts into digestible answers that demonstrate your expertise without overwhelming your interviewer.
Ready to ace that interview? Let’s dive in!
What is ServiceNow ITOM?
Before we jump into the questions, let’s establish a foundation. ServiceNow IT Operations Management (ITOM) is a comprehensive suite of applications that provides visibility into your IT infrastructure and services. It helps organizations discover, manage, and optimize their IT resources through automation and intelligent workflows.
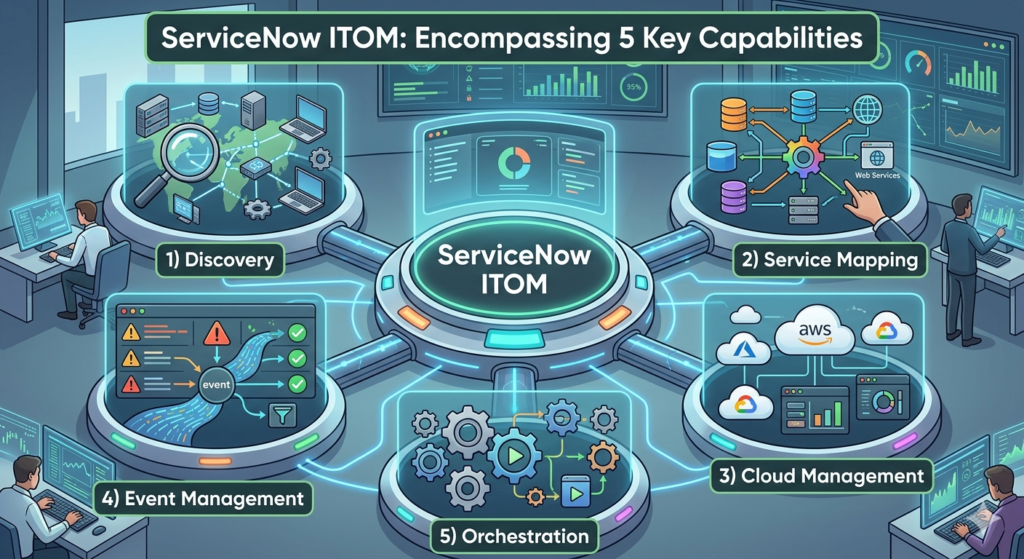
ITOM encompasses several key capabilities:
- Discovery: Automatically identifies IT infrastructure components
- Service Mapping: Visualizes business services and dependencies
- Event Management: Consolidates and manages IT events
- Cloud Management: Governs multi-cloud environments
- Orchestration: Automates IT operations workflows
Top 50 ServiceNow ITOM Interview Questions & Answers
Basic ITOM Concepts (Questions 1-10)
1. What are the core modules of ServiceNow ITOM?
ServiceNow ITOM consists of several integrated modules: Discovery (identifies infrastructure), Service Mapping (maps business services), Event Management (consolidates alerts), Cloud Management (multi-cloud governance), and Orchestration (workflow automation). These modules work together to provide complete visibility and control over IT operations, enabling proactive management and faster incident resolution.
2. How does Discovery work in ServiceNow?
Discovery uses various protocols like SSH, WMI, SNMP, and APIs to scan your network and identify devices, applications, and their relationships. It runs scheduled or on-demand probes that collect configuration data without requiring agents on target systems. The discovered information populates the CMDB, creating an accurate inventory of your IT infrastructure that updates automatically as your environment changes.
3. What is a Configuration Item (CI) in ITOM?
A Configuration Item represents any component in your IT infrastructure that needs to be managed—servers, applications, network devices, or cloud resources. CIs are stored in the Configuration Management Database (CMDB) with attributes like name, status, location, and relationships. Understanding CIs is fundamental because they form the foundation for service mapping, impact analysis, and change management processes.
4. Explain the difference between Discovery and Service Mapping.
Discovery identifies individual infrastructure components (servers, databases, network devices) and stores them as CIs in the CMDB. Service Mapping builds on this by understanding how these components relate to deliver business services. For example, Discovery finds your web servers and databases, while Service Mapping shows how they connect to support your e-commerce application, providing business context to technical infrastructure.
5. What is the CMDB and why is it important?
The Configuration Management Database is the central repository that stores information about all IT assets and their relationships. It’s crucial because it provides a single source of truth for your infrastructure, enabling impact analysis before changes, faster incident resolution, and informed decision-making. A well-maintained CMDB reduces downtime, improves service quality, and supports compliance requirements by maintaining accurate infrastructure documentation.
6. What are the different discovery methods supported by ServiceNow?
ServiceNow supports multiple discovery methods including credential-based discovery (SSH, WMI), credential-less discovery (SNMP), pattern-based discovery for specific applications, cloud discovery for AWS/Azure/GCP, and API-based discovery for SaaS applications. The choice depends on your environment’s security policies, target systems, and the depth of information required. Most organizations use a combination to achieve comprehensive coverage.
7. What is Event Management in ITOM?
Event Management consolidates alerts from multiple monitoring tools into a single platform, applying intelligence to reduce noise and identify genuine issues. It correlates related events, suppresses duplicates, and creates actionable incidents automatically. This prevents alert fatigue, ensures critical issues get immediate attention, and integrates monitoring data with your incident and change processes for better operational efficiency.
8. Define CI Relationship in ServiceNow.
CI Relationships describe how configuration items connect and depend on each other—like “runs on,” “connects to,” or “depends on.” These relationships are critical for impact analysis, showing what services might be affected when a CI fails. For instance, if a database server goes down, relationships reveal which applications and business services will be impacted, enabling proactive communication and prioritized resolution.
9. What is Identification and Reconciliation in Discovery?
Identification determines whether a discovered item is new or already exists in the CMDB by comparing unique attributes. Reconciliation merges data from multiple discovery sources, resolving conflicts and maintaining data accuracy. For example, if Discovery finds a server also imported from your asset management system, reconciliation ensures you have one accurate record, not duplicates, maintaining CMDB integrity.
10. What are MID Servers and why are they used?
Management, Instrumentation, and Discovery (MID) Servers are lightweight applications installed in your network that facilitate communication between ServiceNow and your internal infrastructure. They’re essential because they enable Discovery and Orchestration from cloud-based ServiceNow instances to reach devices behind firewalls, maintaining security while providing automation capabilities. Organizations typically deploy multiple MID Servers for redundancy and geographic distribution.
Intermediate ITOM Questions (Questions 11-30)
11. How do you troubleshoot Discovery issues?
Start by checking MID Server status and logs for connection errors or credential failures. Verify network connectivity and firewall rules allowing required protocols. Review Discovery Status records for specific errors and check credential validity on target systems. Use ECC Queue to monitor communication between MID Server and instance. Most Discovery issues stem from credential problems, network restrictions, or insufficient permissions on target systems.
12. What is Service Mapping, and how does it differ from Application Dependency Mapping?
Service Mapping creates comprehensive maps of business services, showing all infrastructure components and their relationships from top to bottom. Application Dependency Mapping (ADM) focuses specifically on application-level dependencies. Service Mapping is broader, including network, hardware, and business context, while ADM concentrates on application topology. Service Mapping essentially encompasses ADM while providing business service visibility.
13. Explain the concept of Horizontal Discovery.
Horizontal Discovery explores your network broadly, identifying all devices within specified IP ranges without deep application-level details. It’s typically the first discovery phase, creating a baseline inventory of infrastructure. This approach quickly maps your environment’s breadth, identifying servers, network devices, and basic configurations. It’s followed by vertical discovery for deeper application-specific information on critical systems.
14. What are Discovery Patterns?
Discovery Patterns are predefined or custom templates that define how ServiceNow discovers specific applications or technologies. They contain probes, sensors, and identification rules tailored for particular software like Oracle, SAP, or custom applications. Patterns enable deep discovery beyond basic infrastructure, capturing application configurations, versions, and dependencies. ServiceNow provides hundreds of pre-built patterns, and you can create custom ones for proprietary applications.
15. How does Event Management correlation work?
Event Management uses correlation rules to group related events based on criteria like source, time proximity, CI relationships, or message patterns. When multiple events match correlation criteria, they’re linked or merged, reducing duplicate alerts. This intelligence identifies root causes versus symptoms—for instance, a router failure causing hundreds of downstream device alerts gets correlated into one actionable event.
16. What is the difference between Probes and Sensors?
Probes are scripts that run on MID Servers to collect data from target systems using specific protocols like SSH or WMI. Sensors are JavaScript code that runs on the ServiceNow instance to process data collected by probes, creating or updating CIs in the CMDB. Think of probes as data collectors and sensors as data processors that transform raw information into meaningful configuration items.
17. Explain the Service Mapping process.
Service Mapping begins with an entry point (typically a CI representing a business service). It uses Discovery and pattern-based exploration to trace connections from this entry point, identifying all dependent infrastructure—load balancers, application servers, databases, storage. It creates a comprehensive map showing relationships and dependencies. This process can be triggered manually or scheduled, automatically updating as infrastructure changes.
18. What are the key metrics tracked in ITOM?
ITOM tracks metrics including CMDB accuracy percentage, Discovery coverage, CI count and growth, relationship accuracy, event reduction ratio, mean time to detect (MTTD), service mapping completeness, and automation success rates. These metrics help assess ITOM effectiveness, identify areas needing improvement, and demonstrate value to stakeholders. Regular metric reviews ensure your ITOM implementation delivers expected business outcomes.
19. How do you ensure CMDB data quality?
Maintain CMDB quality through regular automated Discovery updates, implementing data governance policies, defining CI ownership, conducting periodic audits, using Identification and Reconciliation rules effectively, and establishing data certification processes. Enable CMDB Health to monitor data quality metrics automatically. Most importantly, treat the CMDB as a product, not a project—continuous maintenance is essential for accuracy.
20. What is Cloud Management in ITOM?
Cloud Management provides visibility and governance across multi-cloud environments (AWS, Azure, GCP). It discovers cloud resources, tracks costs, ensures compliance with policies, optimizes resource utilization, and enables automated provisioning. This module helps organizations manage cloud sprawl, control spending, maintain security standards, and integrate cloud resources into their broader ITOM strategy for hybrid infrastructure visibility.
21. Explain Orchestration in ServiceNow ITOM.
Orchestration automates IT operations tasks by executing workflows across your infrastructure without human intervention. It uses activities like SSH commands, REST API calls, PowerShell scripts, and ServiceNow actions to automate routine tasks—server provisioning, application deployments, remediation workflows. Orchestration reduces manual effort, ensures consistency, speeds up processes, and integrates with Discovery and Event Management for intelligent automation.
22. What are the prerequisites for implementing Service Mapping?
Successful Service Mapping requires an accurate CMDB populated by Discovery, valid credentials for target systems, network access from MID Servers, defined business services as entry points, and appropriate licenses. You also need clear documentation of your service architecture, stakeholder buy-in for ongoing maintenance, and trained personnel. Starting with well-documented, critical business services yields better initial results.
23. How does Health Log Analytics work?
Health Log Analytics collects and analyzes log data from infrastructure components to identify anomalies, predict failures, and provide insights. It uses machine learning to detect patterns indicating potential issues before they cause outages. This proactive approach complements reactive event management, enabling predictive operations. It integrates with Event Management to create incidents automatically when concerning patterns emerge.
24. What is the role of Access Control Lists (ACLs) in ITOM?
ACLs control who can view, create, update, or delete ITOM data like CIs, events, or discovery schedules. Proper ACL configuration ensures sensitive infrastructure information is accessible only to authorized personnel, maintains data integrity by preventing unauthorized changes, and supports compliance requirements. ITOM implementations typically require carefully designed ACLs balancing accessibility with security, especially for privileged infrastructure data.
25. Explain the concept of Service Watch.
Service Watch provides real-time monitoring of business service health by aggregating data from events, alerts, and CI status. It visualizes service health status, shows current incidents affecting services, and highlights dependencies. This business-centric view helps IT teams prioritize issues based on business impact rather than technical severity, improving communication with business stakeholders during outages.
26. What are the common challenges in ITOM implementation?
Common challenges include obtaining valid credentials across diverse infrastructure, managing CMDB data quality, integrating with numerous monitoring tools, justifying ROI to stakeholders, training teams on new processes, handling complex network security restrictions, and maintaining discovery accuracy as infrastructure changes. Successful implementations address these through phased approaches, strong executive sponsorship, dedicated resources, and treating ITOM as ongoing operations, not just implementation.
27. How do you handle credential management for Discovery?
Store credentials securely in ServiceNow’s Credential Registry using appropriate types (SSH, WMI, SNMP, etc.). Implement least-privilege access principles, regularly rotate credentials, monitor credential usage through Discovery logs, and use affinity groups to target specific credentials to appropriate systems. Consider implementing MID Server credential vaults for enhanced security and integrating with enterprise password management systems.
28. What is the purpose of Discovery Schedules?
Discovery Schedules automate regular infrastructure scans, ensuring your CMDB remains current without manual intervention. You can schedule full discoveries for comprehensive updates, quick discoveries for specific CI updates, or service mapping runs for business services. Proper scheduling balances CMDB freshness with network and system load—typically running during off-peak hours with frequencies matching your infrastructure’s change rate.
29. Explain the concept of CI Lifecycle.
CIs progress through lifecycle states: discovered, authorized/approved, active/operational, maintenance, retired, and disposed. Managing this lifecycle ensures your CMDB reflects current reality, removing obsolete items and tracking infrastructure from deployment to decommissioning. Lifecycle management supports accurate reporting, change impact analysis, and compliance by maintaining a true picture of active versus retired infrastructure.
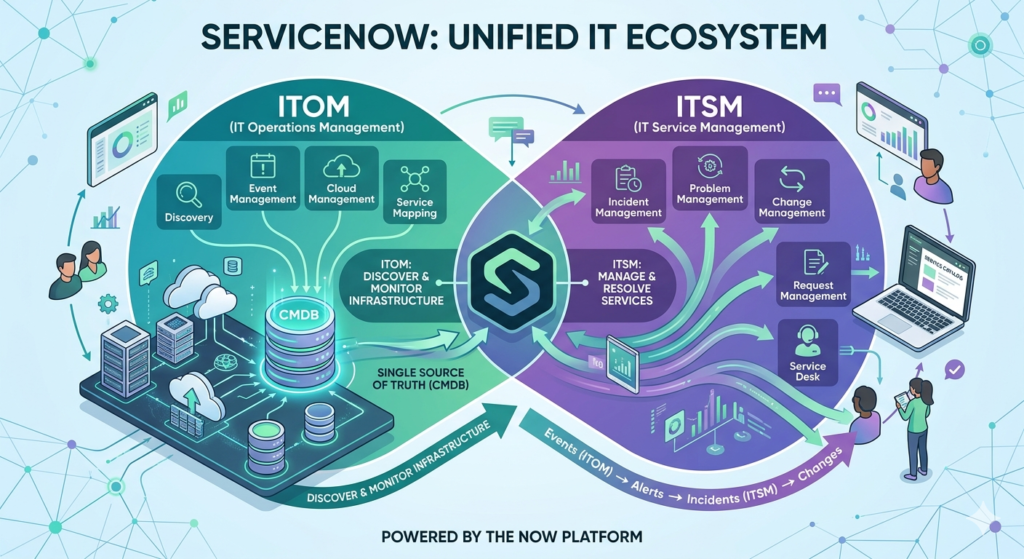
30. What is the relationship between ITOM and ITSM?
ITOM provides the infrastructure visibility and automation foundation that enhances ITSM processes. Discovery and CMDB data improve incident impact analysis and change assessment. Event Management feeds incidents automatically. Service Mapping shows service dependencies for problem management. Together, they create a comprehensive IT management platform where operational data informs service delivery, improving efficiency and service quality.
Advanced ITOM Questions (Questions 31-50)
31. How do you customize Discovery for proprietary applications?
Create custom Discovery patterns by defining probes to collect application-specific data and sensors to process it into CIs. Use pattern designer to map data elements to CI attributes and relationships. Test patterns in development environments before production deployment. Document custom patterns thoroughly and maintain them as applications evolve. This customization ensures your CMDB accurately represents your complete environment.
32. Explain Traffic-Based Service Mapping.
Traffic-Based Service Mapping analyzes actual network traffic patterns to discover service dependencies automatically, complementing pattern-based discovery. It observes communication between systems to infer relationships without requiring credentials for every system. This approach discovers undocumented dependencies and validates service maps against real behavior. It’s particularly valuable for complex environments where documentation is incomplete or outdated.
33. What are the best practices for MID Server deployment?
Deploy multiple MID Servers for redundancy and load distribution. Position them network-logically near discovery targets to minimize latency. Allocate adequate resources (4GB RAM minimum, dedicated cores). Implement monitoring of MID Server health and performance. Separate MID Servers by function (discovery, orchestration) or security zone. Keep them updated with latest versions and maintain secure credential storage.
34. How do you measure ITOM ROI?
Measure ROI through quantifiable metrics: reduced MTTR from better visibility, fewer change-related incidents due to impact analysis, time saved through automation, reduced duplicate alerts from event correlation, improved compliance, and optimized cloud spending. Track before-and-after comparisons of these metrics. Calculate cost savings from prevented outages and efficiency gains versus ITOM investment for compelling business cases.
35. What is the role of CMDB Health Dashboard?
CMDB Health Dashboard provides visibility into data quality, completeness, compliance, correctness, and duplication. It identifies issues like CIs missing required attributes, duplicate records, or stale data. Regular monitoring through this dashboard enables proactive data quality management. It helps prioritize cleanup efforts and demonstrates CMDB health improvement over time to stakeholders.
36. Explain the integration between ITOM and ITBM.
ITOM provides technical infrastructure data that informs IT Business Management (ITBM) decisions. CMDB data supports project portfolio decisions by showing resource availability and capacity. Cloud cost information from ITOM feeds financial planning. Orchestration automates project provisioning. This integration ensures technical realities inform business decisions and strategic planning considers operational constraints.
37. How do you handle multi-tenancy in ITOM?
Multi-tenancy separates data for different business units or customers using domain separation. Configure Discovery schedules per domain, implement domain-specific credentials, and set appropriate ACLs. Ensure MID Servers respect domain boundaries. Service Mapping should maintain domain isolation while allowing controlled sharing of common infrastructure. Proper multi-tenant configuration maintains data privacy while enabling operational efficiency.
38. What is Predictive AIOps in ServiceNow?
Predictive AIOps uses machine learning to predict incidents before they occur, recommend solutions based on historical patterns, and automate remediation. It analyzes event patterns, CI changes, and incident history to identify emerging issues. This proactive approach reduces downtime, enables preventive action, and continuously improves as it learns from your environment’s behavior.
39. How do you ensure Discovery performance optimization?
Optimize Discovery by limiting scope to necessary IP ranges, scheduling during off-peak hours, tuning probe timeout values, using Quick Discovery for targeted updates, distributing load across multiple MID Servers, and excluding known unresponsive IPs. Monitor Discovery performance metrics and ECC Queue depths. Optimize patterns by removing unnecessary data collection and leveraging parallel processing.
40. Explain the concept of CI Classes and their hierarchy.
CI Classes define types of configuration items with specific attributes and relationships—like Server, Database, Application. They’re organized hierarchically where child classes inherit parent attributes. For example, Linux Server inherits from Server, which inherits from Computer. Understanding this hierarchy is crucial for customization, reporting, and ensuring consistent data modeling across your CMDB.
41. What security considerations apply to ITOM?
ITOM security involves protecting credentials with encryption and vaults, controlling CMDB access through ACLs, securing MID Server communication with mutual authentication, monitoring Discovery activity logs for anomalies, implementing least-privilege principles, and ensuring compliance with data protection regulations. Consider network segmentation for MID Servers and regular security audits of ITOM configurations.
42. How do you handle Discovery in containerized environments?
Discovering containers requires specialized approaches due to their ephemeral nature. ServiceNow provides patterns for Docker, Kubernetes, and OpenShift that continuously discover container infrastructure, pods, services, and dependencies. Integration with container orchestration platforms through APIs enables real-time tracking. Consider whether to track individual containers or focus on services and orchestration components.
43. What is the role of transform maps in ITOM?
Transform maps process data from external sources (integrations, imports) into ServiceNow tables, particularly the CMDB. They define field mappings, coalesce fields for matching existing records, and can execute scripts for complex transformations. In ITOM contexts, transform maps integrate data from asset management systems, monitoring tools, or cloud platforms, enriching Discovery data.
44. Explain Event Management automation capabilities.
Event Management automates incident creation based on event severity and correlation, assigns incidents to appropriate groups using assignment rules, triggers remediation workflows through Orchestration, and implements self-healing for known issues. It can automatically close events when monitoring systems report resolution and escalate unacknowledged critical events. This automation reduces manual effort and accelerates response.
45. How do you approach Service Mapping for microservices architectures?
Microservices mapping requires continuous discovery due to dynamic scaling and deployment. Focus on service-level mapping rather than individual container instances. Integrate with service meshes and API gateways to understand service communication. Use traffic-based discovery to capture actual dependencies. Emphasize logical service relationships over physical infrastructure, and implement automated mapping triggered by deployment pipelines.
46. What is the difference between Quick Discovery and Full Discovery?
Quick Discovery targets specific CIs for rapid updates, executing limited probes to refresh specific attributes without comprehensive exploration. Full Discovery performs complete infrastructure scans, running all applicable probes and patterns. Use Quick Discovery for targeted updates after changes or on-demand verification, and Full Discovery for comprehensive CMDB refreshes. This combination balances accuracy with performance.
47. How do you implement disaster recovery for ITOM?
Disaster recovery for ITOM involves backing up MID Server configurations, documenting deployment procedures, maintaining credential backups (securely), replicating ServiceNow instance data through platform backups, documenting integration configurations, and testing MID Server redeployment procedures. Consider geographic distribution of MID Servers for resilience. ITOM’s cloud-based nature simplifies DR compared to on-premise alternatives.
48. Explain the relationship between ITOM and SecOps.
ITOM provides the infrastructure visibility foundation that enhances security operations. Discovery identifies all assets, including shadow IT. CMDB data enriches security incident context. Vulnerability Response integrates with ITOM to correlate vulnerabilities with actual infrastructure. Event Management can ingest security alerts. Service Mapping shows potential breach impact paths. Together, they enable security-aware operations.
49. What are identification rules and why are they important?
Identification rules determine whether a discovered item matches an existing CI or represents a new one by comparing unique identifiers like serial numbers, MAC addresses, or FQDNs. Accurate identification prevents CMDB duplication and ensures Discovery updates existing records rather than creating duplicates. Well-designed identification rules are crucial for CMDB data quality and accurate infrastructure representation.
50. How do you stay current with ServiceNow ITOM updates?
Stay current by regularly reviewing ServiceNow release notes and Now Learning platform courses, participating in ServiceNow Community discussions, attending Knowledge conferences and local user groups, following ServiceNow blogs and YouTube channel, practicing in Personal Developer Instances with new features, and obtaining relevant certifications. The platform evolves rapidly, making continuous learning essential for ITOM professionals.
Ready to Launch Your ServiceNow ITOM Career?
Armed with these 50 essential interview questions and answers, you’re well-prepared to demonstrate your ServiceNow ITOM expertise. Remember, interviews aren’t just about memorizing answers—they’re about showing your understanding and passion for IT operations excellence.
Take the next step:
- Practice these questions with a colleague or mentor
- Explore ServiceNow’s Personal Developer Instance for hands-on experience
- Join the ServiceNow Community to connect with ITOM professionals
- Share this guide with others preparing for ITOM interviews
Got questions or want to share your interview experience? Drop a comment below—we’d love to hear from you!
Related Articles:
- Complete Guide to ServiceNow Discovery Best Practices
- CMDB Management Strategies
- ServiceNow Certification Path: From Beginner to Expert
Connect with RizeX Labs:
For personalized ServiceNow training and consultation, contact our experts today and accelerate your ITOM journey!

Quick Summary
ServiceNow ITOM is a powerful suite transforming IT operations through automated discovery, intelligent event management, and comprehensive service mapping. Success in ITOM roles requires understanding core concepts like CMDB management, Discovery mechanisms, and Service Mapping principles, combined with practical skills in configuration, troubleshooting, and integration. This guide's 50 questions cover fundamental concepts for beginners, intermediate operational knowledge, and advanced topics like microservices mapping and AIOps. Continuous learning, hands-on practice, and staying current with platform updates are essential for ITOM career growth. Master these concepts, practice articulating answers clearly, and approach interviews with confidence in your ITOM expertise.

