Introduction to Salesforce Security Model
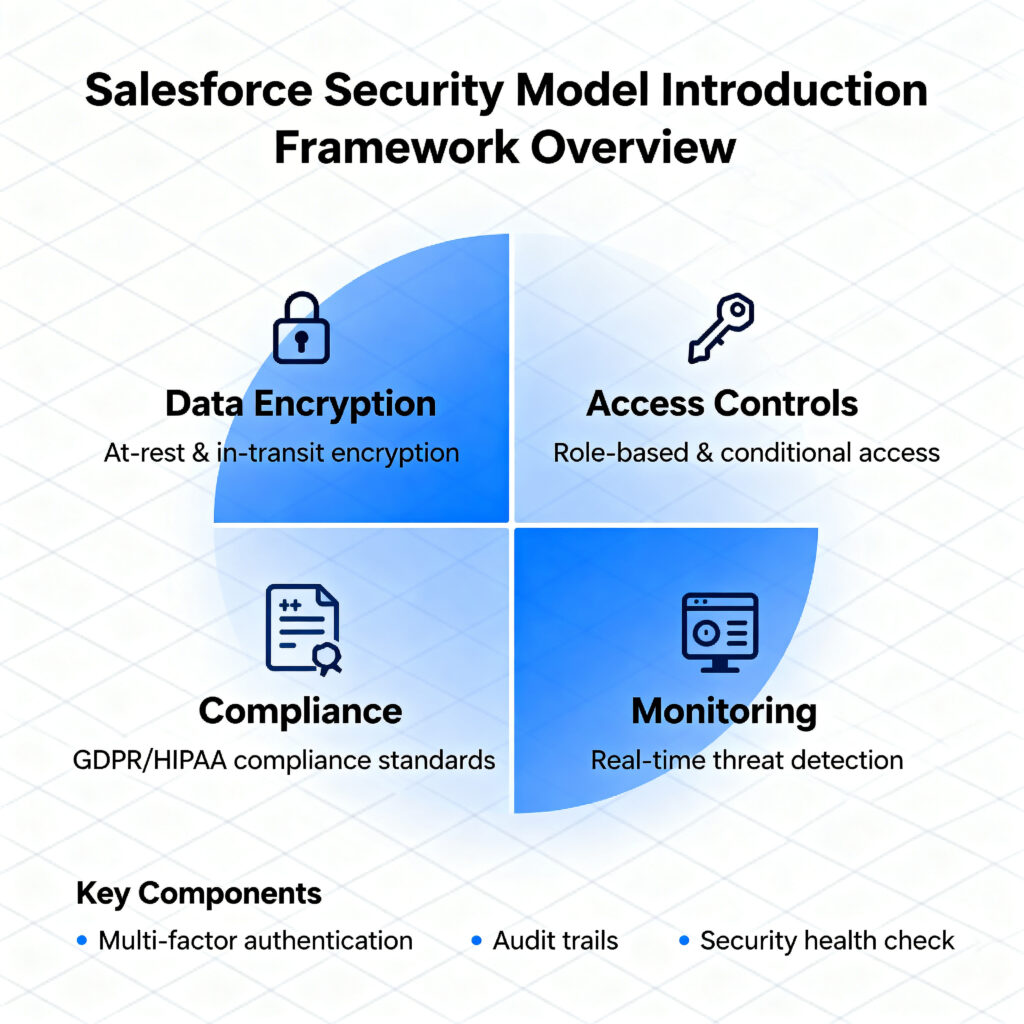
Salesforce Security Model is the comprehensive framework that protects your organization’s most valuable asset – customer data. Understanding Salesforce Security Model is essential for every Salesforce professional, from administrators to executives.
At RizeX Labs, we recognize that Salesforce Security Model can seem complex at first. This guide breaks down Salesforce Security Model into manageable components, showing how each piece works together. Whether you’re implementing Salesforce Security Model for the first time or optimizing existing configurations, this comprehensive guide covers everything you need.
Salesforce Security Model operates on a principle of layered security, where multiple controls work together. When properly implemented, Salesforce Security Model ensures only authorized users access appropriate data while maintaining operational efficiency.
Why Understanding Salesforce Security Model is Critical
- Data Protection: Salesforce Security Model prevents unauthorized data access
- Compliance: Proper Salesforce Security Model implementation ensures regulatory adherence
- User Productivity: Balanced Salesforce Security Model enables efficient workflows
- Risk Mitigation: Well-designed Salesforce Security Model reduces security incidents
- Organizational Trust: Salesforce Security Model demonstrates commitment to data safety
What is Salesforce Security Model – Complete Overview
Salesforce Security Model is a multi-layered framework controlling data access at multiple levels. Understanding Salesforce Security Model means recognizing these distinct layers work together.
Salesforce Security Model Definition
Salesforce Security Model defines who can access what data, when, and how. The architecture of Salesforce Security Model includes five primary layers, each serving specific purposes in the overall security framework of Salesforce Security Model.
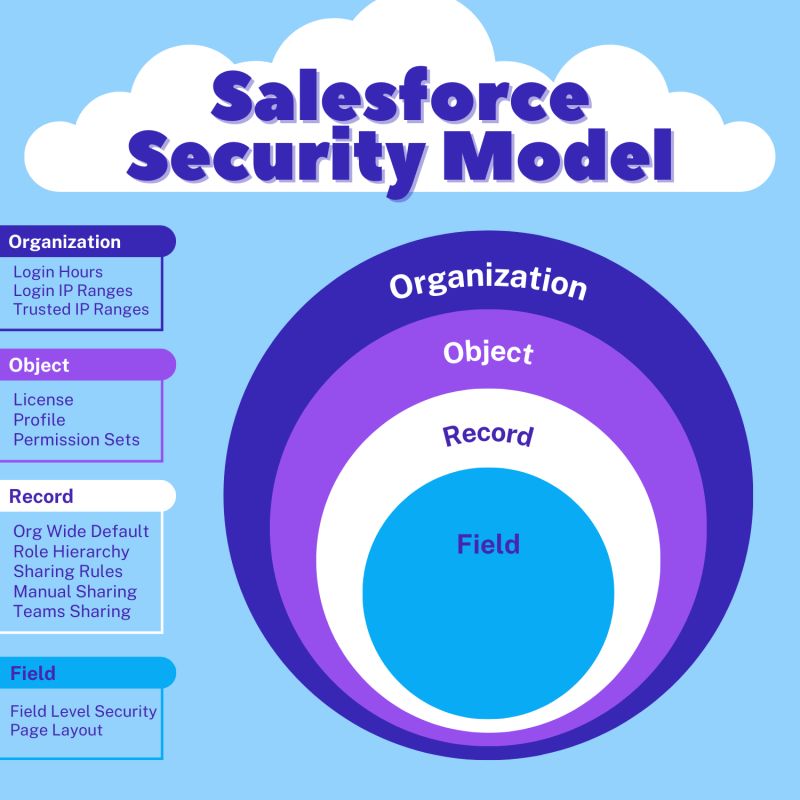
The Five-Layer Architecture of Salesforce Security Model
Layer 1: Organizational Access
Foundation of Salesforce Security Model controlling who enters your Salesforce instance.
Layer 2: Organization-Wide Defaults (OWD)
Core of Salesforce Security Model setting default record access permissions in the Salesforce Security Model framework.
Layer 3: Role Hierarchy
Management component of Salesforce Security Model creating organizational structure within Salesforce Security Model.
Layer 4: Sharing Rules
Flexibility component of Salesforce Security Model allowing exceptions to default settings in Salesforce Security Model.
Layer 5: Profiles and Permission Sets
Feature and object control in Salesforce Security Model managing what users can do within Salesforce Security Model.
How Salesforce Security Model Protects Data
Multi-Level Control in Salesforce Security Model
Salesforce Security Model uses multiple control points to ensure comprehensive protection within Salesforce Security Model:
- Record-level security (OWD and sharing)
- Object-level security (Profiles)
- Field-level security (Field permissions)
- Feature-level security (System permissions)
This layered approach in Salesforce Security Model provides defense in depth.
Salesforce Security Model vs Traditional Security
| Aspect | Traditional Model | Salesforce Security Model |
| Control Type | Control Type | Layered approach in Salesforce Security Model |
| Flexibility | Rigid | Adaptable Salesforce Security Model |
| Scalability | Limited | Scales in Salesforce Security Model |
| Management | Complex | Simplified Salesforce Security Model |
| User Experience | Often restrictive | Balanced in Salesforce Security Model |
The advantage of Salesforce Security Model is its balanced approach to security and usability.
Why Salesforce Security Model Matters for Your Organization

Organizations implementing proper Salesforce Security Model see measurable benefits. Understanding why Salesforce Security Model matters drives successful implementation.
Data Protection Through Salesforce Security Model
Preventing Unauthorized Access
Salesforce Security Model prevents employees from accessing data outside their responsibilities. Proper Salesforce Security Model configuration protects:
- Customer personal information
- Confidential business data
- Proprietary strategies
- Financial information
Regulatory Compliance Through Salesforce Security Model
Meeting Compliance Requirements
Salesforce Security Model helps organizations meet:
- GDPR: Salesforce Security Model ensures data protection compliance
- HIPAA: Salesforce Security Model protects healthcare data
- CCPA: Salesforce Security Model enables privacy requirements
- SOX: Salesforce Security Model provides audit trails
- Industry Standards: Salesforce Security Model adapts to specific requirements
Operational Efficiency with Salesforce Security Model
Balancing Security and Productivity
Well-designed Salesforce Security Model enables user productivity while maintaining security. Excessive restrictions in Salesforce Security Model hinder work, while insufficient controls in Salesforce Security Model create risks.
Financial Impact of Salesforce Security Model
Cost of Security Breaches
Organizations without proper Salesforce Security Model face:
- Data breach costs averaging $3-5 million
- Regulatory fines and penalties
- Reputation damage
- Loss of customer trust
Implementing Salesforce Security Model prevents these costs.
Layer 1: Understanding Salesforce Security Model Foundation
The foundation of Salesforce Security Model rests on core security principles. Understanding these principles shapes proper Salesforce Security Model implementation.
Core Principles of Salesforce Security Model
Principle of Least Privilege in Salesforce Security Model
Users should have minimum access necessary to perform their jobs. This principle guides all Salesforce Security Model decisions:
- Don’t grant unnecessary access in Salesforce Security Model
- Review and remove excessive permissions in Salesforce Security Model
- Regularly audit Salesforce Security Model configurations
Defense in Depth Approach to Salesforce Security Model
Multiple security layers in Salesforce Security Model mean one layer failing doesn’t compromise everything. Salesforce Security Model architecture includes:
- Organization-level controls in Salesforce Security Model
- Record-level restrictions in Salesforce Security Model
- Field-level masking in Salesforce Security Model
- Audit trails throughout Salesforce Security Model
User Hierarchy in Salesforce Security Model
Understanding User Roles
Roles create organizational structure within Salesforce Security Model:
- Executives at top
- Managers in middle
- Team members at bottom
- Roles define default visibility in Salesforce Security Model
Profile Assignment in Salesforce Security Model
Profiles within Salesforce Security Model define capabilities:
- What objects users access
- What fields users see
- What features users utilize
- What actions users perform in Salesforce Security Model
Data Classification for Salesforce Security Model
Categorizing Data in Salesforce Security Model
Effective Salesforce Security Model requires classifying data:
- Public Data: Accessible to most users in Salesforce Security Model
- Internal Data: Limited to specific departments within Salesforce Security Model
- Confidential: Restricted to authorized users in Salesforce Security Model
- Highly Sensitive: Maximum protection within Salesforce Security Model
This classification drives Salesforce Security Model configuration decisions.
Salesforce Security Model Architecture Overview
Five-Layer Stack of Salesforce Security Model
Each layer in Salesforce Security Model serves distinct purposes:
Organizational Security (Layer 1):
- Login controls in Salesforce Security Model
- IP restrictions within Salesforce Security Model
- Session management in Salesforce Security Model
Record Access (Layers 2-4):
- OWD defaults in Salesforce Security Model
- Role hierarchy visibility in Salesforce Security Model
- Sharing rules flexibility in Salesforce Security Model
Feature/Field Access (Layer 5):
- Profiles and permissions in Salesforce Security Model
- Field-level security in Salesforce Security Model
- System permissions in Salesforce Security Model
Layer 2: Organization-Wide Defaults in Salesforce Security Model
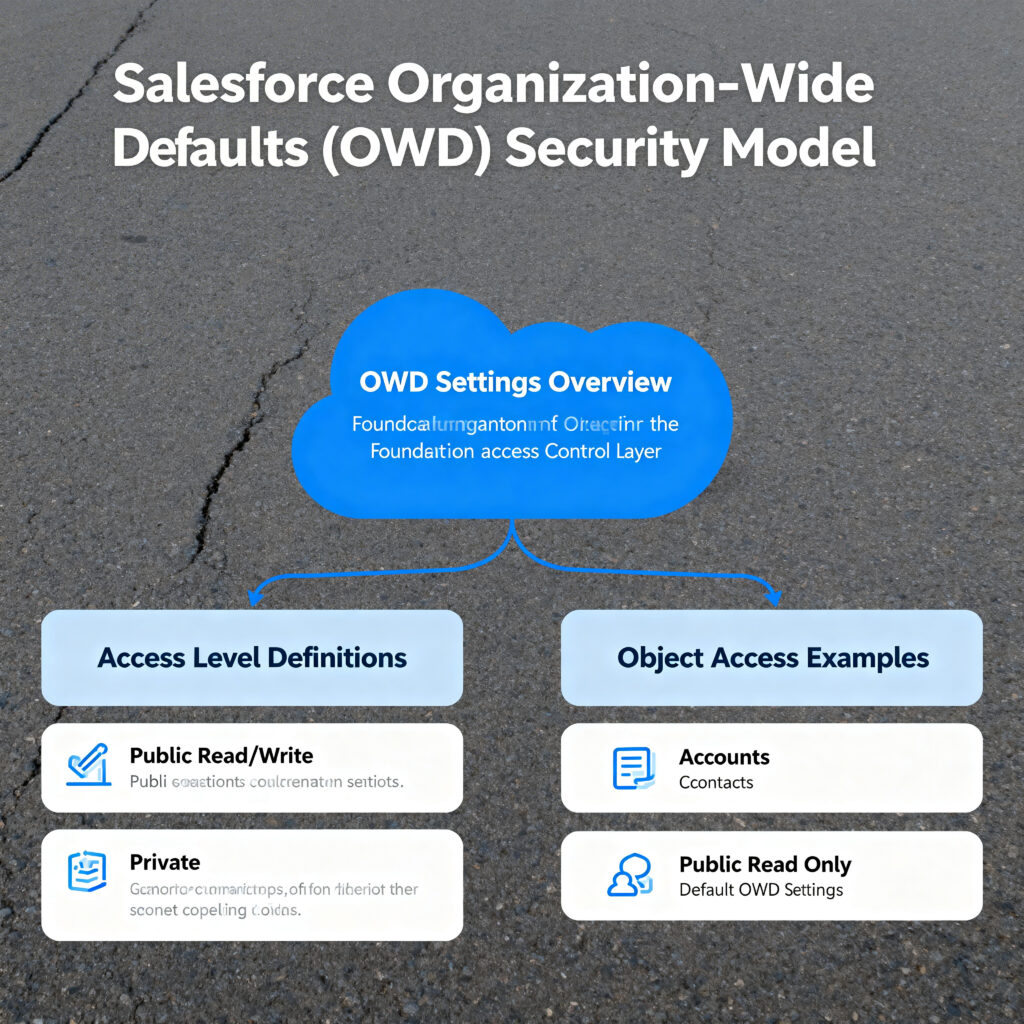
Organization-Wide Defaults (OWD) form the foundation of Salesforce Security Model, establishing default record access permissions within Salesforce Security Model.
Understanding OWD in Salesforce Security Model
OWD Definition in Salesforce Security Model
Organization-Wide Defaults within Salesforce Security Model define the default level of access users have to records they don’t own. OWD is foundational to Salesforce Security Model architecture.
Why OWD Matters in Salesforce Security Model
OWD settings in Salesforce Security Model determine:
- Who sees what records by default
- Starting point for all Salesforce Security Model sharing
- Balance between security and access in Salesforce Security Model
- Foundation for sharing rules in Salesforce Security Model
OWD Settings in Salesforce Security Model
Public Read/Write in Salesforce Security Model
Most permissive OWD setting within Salesforce Security Model:
- All users see and modify all records
- Simplest configuration in Salesforce Security Model
- Highest risk setting in Salesforce Security Model
- Limited sharing rules needed in Salesforce Security Model
Public Read Only in Salesforce Security Model
Balanced OWD setting within Salesforce Security Model:
- All users see all records
- Only owners modify in Salesforce Security Model
- Common configuration in Salesforce Security Model
- Works well for reporting in Salesforce Security Model
Private in Salesforce Security Model
Most restrictive OWD setting within Salesforce Security Model:
- Users only see own records by default
- All access via sharing in Salesforce Security Model
- Maximum security in Salesforce Security Model
- Requires extensive sharing rules in Salesforce Security Model
Controlled by Parent in Salesforce Security Model
Dependent OWD setting within Salesforce Security Model:
- Access depends on parent record access
- Used for master-detail relationships in Salesforce Security Model
- Simplifies hierarchy in Salesforce Security Model
- Automatic inheritance in Salesforce Security Model
Configuring OWD in Salesforce Security Model
Setting OWD Properly in Salesforce Security Model
- Go to Setup → Sharing Settings in Salesforce Security Model
- Select object to configure in Salesforce Security Model
- Choose OWD setting appropriate for Salesforce Security Model data sensitivity
- Configure external access visibility in Salesforce Security Model
- Save settings and verify in Salesforce Security Model
OWD Examples in Salesforce Security Model
Sales Organization Example in Salesforce Security Model
- Accounts: Public Read Only (entire team needs account visibility)
- Opportunities: Private (managers control team opportunity visibility through Salesforce Security Model)
- Contacts: Public Read Only (shared customer contact database in Salesforce Security Model)
This configuration in Salesforce Security Model enables collaboration while protecting opportunity data.
Service Organization Example in Salesforce Security Model
- Cases: Private (agents only see assigned cases by default in Salesforce Security Model)
- Solutions: Public Read Only (shared knowledge base in Salesforce Security Model)
- Knowledge: Public Read Only (customer-facing content in Salesforce Security Model)
This setup in Salesforce Security Model balances case privacy with knowledge sharing in Salesforce Security Model.
OWD Best Practices in Salesforce Security Model
Start Restrictive in Salesforce Security Model
Begin with Private OWD in Salesforce Security Model. Open access using sharing rules rather than restricting later when using Salesforce Security Model.
Document OWD Decisions in Salesforce Security Model
Record why each OWD was chosen in Salesforce Security Model. Documentation in Salesforce Security Model helps future configuration changes.
Review OWD Quarterly in Salesforce Security Model
Regular reviews in Salesforce Security Model ensure settings still match business needs. Quarterly audits in Salesforce Security Model prevent security drift.
Layer 3: Role Hierarchy in Salesforce Security Model
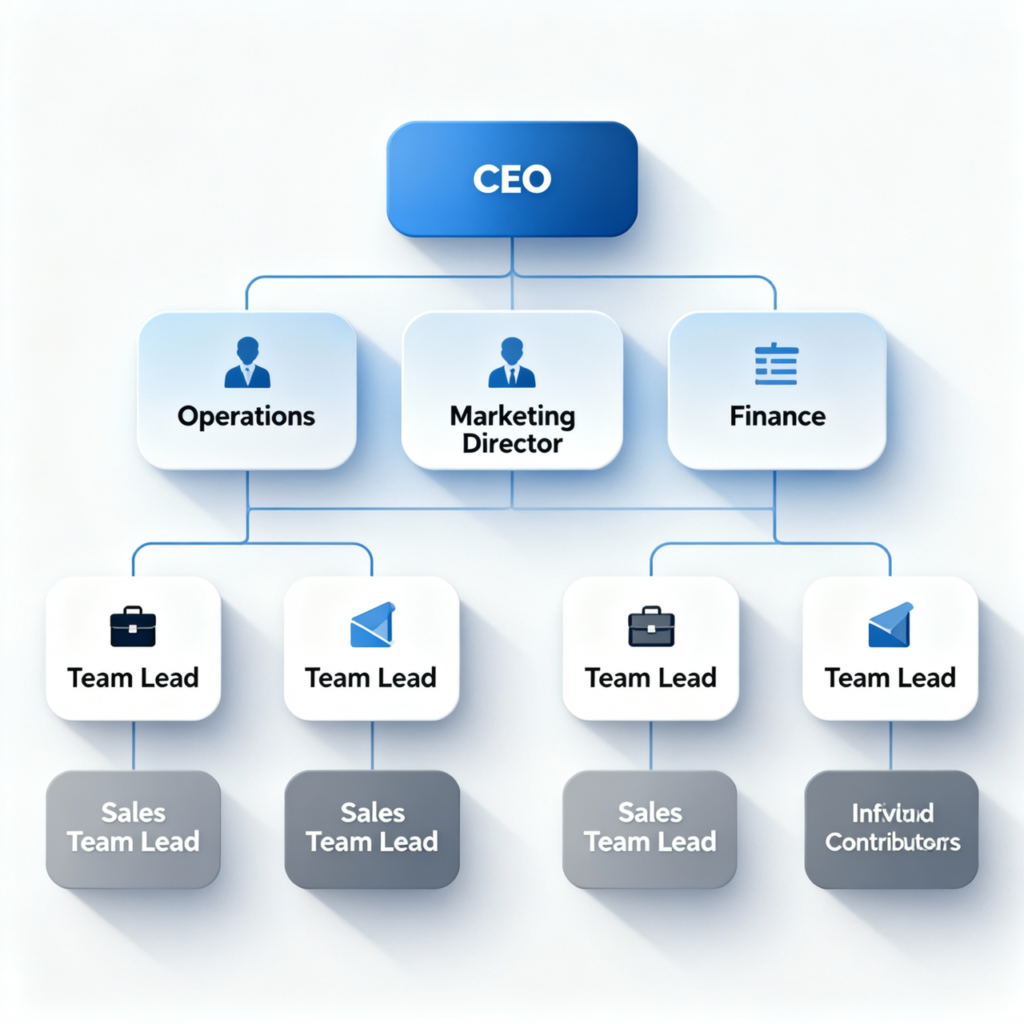
Role hierarchy creates organizational structure within Salesforce Security Model, enabling automatic record visibility in Salesforce Security Model.
Understanding Role Hierarchy in Salesforce Security Model
Role Hierarchy Concept in Salesforce Security Model
Role hierarchy in Salesforce Security Model creates organization structure where higher roles automatically see lower roles’ records. This inheritance mechanism in Salesforce Security Model simplifies access management.
Why Role Hierarchy Matters in Salesforce Security Model
Role hierarchy in Salesforce Security Model:
- Reflects organizational structure in Salesforce Security Model
- Enables manager visibility automatically in Salesforce Security Model
- Scales with organization in Salesforce Security Model
- Simplifies access management in Salesforce Security Model
Designing Role Hierarchy for Salesforce Security Model
Matching Organizational Structure in Salesforce Security Model
Design role hierarchy in Salesforce Security Model to mirror actual organization:
- Executive roles at top
- Manager roles in middle
- Individual contributor roles at bottom
- Accurate hierarchy in Salesforce Security Model reflects reality
Role Naming Conventions for Salesforce Security Model
Use clear names when creating Salesforce Security Model roles:
- “VP Sales” instead of “VP_S”
- “Sales Manager – North” instead of “SM_N”
- Clear names in Salesforce Security Model improve understanding
Avoiding Unnecessary Complexity in Salesforce Security Model
Keep role hierarchy in Salesforce Security Model simple:
- 3-5 levels works for most organizations in Salesforce Security Model
- Deeper hierarchies complicate Salesforce Security Model
- Avoid creating roles for theoretical positions in Salesforce Security Model
Role Hierarchy Configuration in Salesforce Security Model
Creating Roles in Salesforce Security Model
- Navigate Setup → Users → Roles in Salesforce Security Model
- Click “Create New Role” in Salesforce Security Model
- Enter role name and parent role in Salesforce Security Model
- Configure role properties in Salesforce Security Model
- Save and assign users in Salesforce Security Model
Role Hierarchy Examples in Salesforce Security Model
Sales Organization Example in Salesforce Security Model
CEO
├── VP Sales (sees all)
│ ├── Regional Manager - North (sees North)
│ │ ├── Sales Rep 1
│ │ └── Sales Rep 2
│ └── Regional Manager - South (sees South)
│ ├── Sales Rep 3
│ └── Sales Rep 4In this Salesforce Security Model structure, VP Sales automatically sees all records. Regional managers see their team’s records. This hierarchy in Salesforce Security Model enables appropriate visibility.
Service Organization Example in Salesforce Security Model
Support Director
├── Support Manager
│ ├── Agent 1
│ └── Agent 2
└── Technical Manager
├── Tech Agent 1
└── Tech Agent 2Director sees all in this Salesforce Security Model arrangement. Managers see only their team’s cases in Salesforce Security Model.
Role Hierarchy Limitations in Salesforce Security Model
Single Manager Per Role in Salesforce Security Model
Users report to one manager in Salesforce Security Model. Matrix reporting requires sharing rules in Salesforce Security Model.
Cannot Restrict in Salesforce Security Model
Role hierarchy in Salesforce Security Model only grants access. Restriction requires OWD or sharing rules in Salesforce Security Model.
Role Hierarchy Best Practices in Salesforce Security Model
Regular Review in Salesforce Security Model
Review role hierarchy in Salesforce Security Model quarterly as organization changes in Salesforce Security Model.
Document Changes in Salesforce Security Model
Record why role hierarchy changes in Salesforce Security Model. Documentation in Salesforce Security Model helps future administrators understand Salesforce Security Model decisions.
Layer 4: Sharing Rules Within Salesforce Security Model
Sharing rules provide flexibility within Salesforce Security Model, allowing exceptions and cross-functional access in Salesforce Security Model.
Understanding Sharing Rules in Salesforce Security Model
Sharing Rules Definition in Salesforce Security Model
Sharing rules within Salesforce Security Model grant additional access beyond OWD and role hierarchy in Salesforce Security Model. They enable flexibility in Salesforce Security Model.
When to Use Sharing Rules in Salesforce Security Model
Deploy sharing rules in Salesforce Security Model when:
- Cross-functional teams need access in Salesforce Security Model
- Role hierarchy doesn’t cover all scenarios in Salesforce Security Model
- Territory-based sharing needed in Salesforce Security Model
- Public group access required in Salesforce Security Model
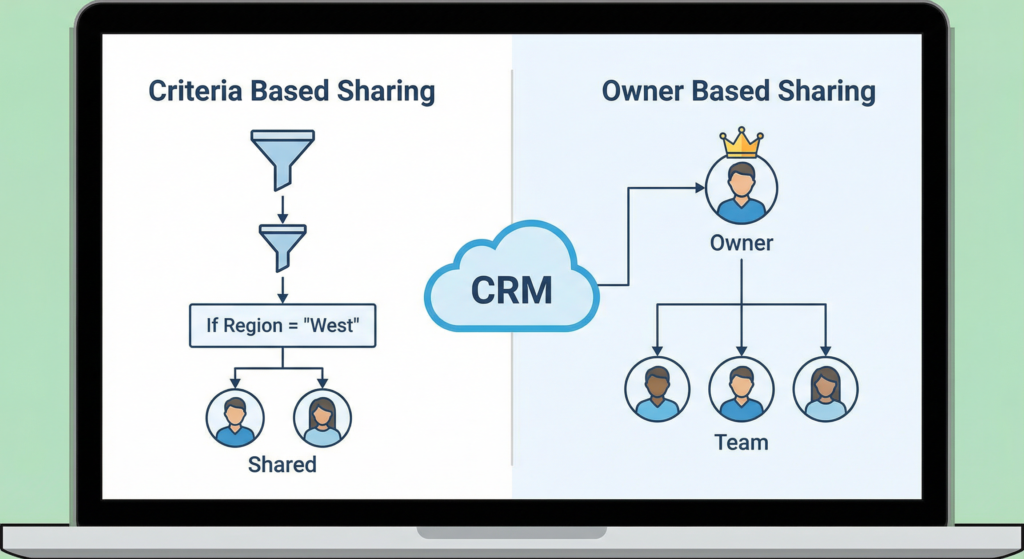
Types of Sharing Rules in Salesforce Security Model
User-Based Sharing Rules in Salesforce Security Model
Share based on user characteristics in Salesforce Security Model:
- Specific users in Salesforce Security Model
- Department membership in Salesforce Security Model
- Role assignments in Salesforce Security Model
- Simple user-based sharing in Salesforce Security Model
Criteria-Based Sharing Rules in Salesforce Security Model
Share based on record field values in Salesforce Security Model:
- Share where Region = “North” in Salesforce Security Model
- Share where Status = “Active” in Salesforce Security Model
- Field value matching in Salesforce Security Model
- Flexible criteria in Salesforce Security Model
Creating Sharing Rules in Salesforce Security Model
Implementing Sharing Rules in Salesforce Security Model
- Go to Setup → Sharing Settings in Salesforce Security Model
- Click “Create” under Sharing Rules in Salesforce Security Model
- Choose sharing rule type in Salesforce Security Model
- Define who shares and with whom in Salesforce Security Model
- Set access level (Read, Read/Write) in Salesforce Security Model
- Save and test in Salesforce Security Model
Sharing Rules Examples in Salesforce Security Model
Territory-Based Sharing in Salesforce Security Model
- Share all Opportunities where Region = “East”
- With: Eastern Sales Team
- Access: Read/Write
- Purpose: Ensure all east region visibility in Salesforce Security Model
Cross-Functional Sharing in Salesforce Security Model
- Share all Cases where Priority = “High”
- With: Management Group
- Access: Read Only
- Purpose: Leadership oversight in Salesforce Security Model
Sharing Rules Best Practices in Salesforce Security Model
Keep Simple in Salesforce Security Model
Simpler rules in Salesforce Security Model are easier to understand and maintain in Salesforce Security Model.
Document All Rules in Salesforce Security Model
Record why each rule exists in Salesforce Security Model. Documentation in Salesforce Security Model helps future changes.
Avoid Overlapping Rules in Salesforce Security Model
Check for overlapping sharing in Salesforce Security Model. Overlaps in Salesforce Security Model create confusion.
Review Quarterly in Salesforce Security Model
Remove outdated rules in Salesforce Security Model. Quarterly review in Salesforce Security Model prevents security drift.
Layer 5: Profiles and Permission Sets in Salesforce Security Model
Profiles and permission sets control object and feature access within Salesforce Security Model, forming the fifth layer.
Understanding Profiles in Salesforce Security Model
Profiles Definition in Salesforce Security Model
Profiles in Salesforce Security Model define what licensed users can do:
- Object permissions in Salesforce Security Model
- Field permissions in Salesforce Security Model
- Tab visibility in Salesforce Security Model
- System permissions in Salesforce Security Model
Standard Profiles in Salesforce Security Model
Salesforce provides standard profiles in Salesforce Security Model:
- System Administrator in Salesforce Security Model
- Sales User in Salesforce Security Model
- Service Cloud User in Salesforce Security Model
- Partner Community in Salesforce Security Model
Custom Profiles in Salesforce Security Model
Create custom profiles in Salesforce Security Model when standard profiles don’t match needs in Salesforce Security Model.
Understanding Permission Sets in Salesforce Security Model
Permission Sets Definition in Salesforce Security Model
Permission sets in Salesforce Security Model add additional access to profiles in Salesforce Security Model. They never restrict access in Salesforce Security Model.
Permission Sets Benefits in Salesforce Security Model
Permission sets in Salesforce Security Model:
- Avoid creating multiple profiles in Salesforce Security Model
- Handle exceptions easily in Salesforce Security Model
- Can be temporary in Salesforce Security Model
- Simplify management in Salesforce Security Model
Profiles vs Permission Sets in Salesforce Security Model
| Aspect | Profiles | Permission Sets |
| Primary Role | Main access | Additional access |
| Restriction | Can restrict | Only add access |
| Users per profile | One | Many |
| When to use | Foundation | Exceptions |
| Management | Complex | Simple |
Understanding this distinction in Salesforce Security Model improves design choices.
Configuring Profiles in Salesforce Security Model
Profile Configuration Steps in Salesforce Security Model
- Go to Setup → Users → Profiles in Salesforce Security Model
- Select or create profile in Salesforce Security Model
- Configure object permissions in Salesforce Security Model
- Set field-level permissions in Salesforce Security Model
- Configure system permissions in Salesforce Security Model
- Save and assign users in Salesforce Security Model
System Permissions in Salesforce Security Model
Important System Permissions in Salesforce Security Model
Control sensitive actions in Salesforce Security Model:
- “Modify All Data” in Salesforce Security Model
- “View All Data” in Salesforce Security Model
- “Manage Users” in Salesforce Security Model
- “Export Data” in Salesforce Security Model
- “API Enabled” in Salesforce Security Model
Grant these carefully in Salesforce Security Model.
Field-Level Security in Salesforce Security Model

Field-level security provides granular data protection within Salesforce Security Model, hiding sensitive fields.
Understanding Field-Level Security in Salesforce Security Model
Field-Level Security Concept in Salesforce Security Model
Field-level security in Salesforce Security Model controls which users see which fields. This granularity in Salesforce Security Model protects sensitive information.
Implementing Field-Level Security in Salesforce Security Model
Profile-Based Field Security in Salesforce Security Model
Control field visibility through profiles in Salesforce Security Model:
- Go to Profiles in Salesforce Security Model
- Find Field-Level Security section in Salesforce Security Model
- Set Read/Edit permissions for fields in Salesforce Security Model
- Save in Salesforce Security Model
Encryption in Salesforce Security Model
Transparent Data Encryption in Salesforce Security Model
Encrypt fields automatically in Salesforce Security Model:
- Works transparently in Salesforce Security Model
- Maximum field protection in Salesforce Security Model
- Prevents field searches in Salesforce Security Model
Shield Encryption in Salesforce Security Model
Customer-managed encryption in Salesforce Security Model:
- Customer controls keys in Salesforce Security Model
- Enhanced security in Salesforce Security Model
- Additional cost in Salesforce Security Model
Salesforce Security Model Best Practices and Strategies
Following proven practices ensures successful Salesforce Security Model implementation.
Documentation for Salesforce Security Model
Access Matrix in Salesforce Security Model
Document who accesses what in Salesforce Security Model:
- Users in Salesforce Security Model
- Objects accessed in Salesforce Security Model
- Permission levels in Salesforce Security Model
- Updated quarterly in Salesforce Security Model
Change Documentation in Salesforce Security Model
Record all Salesforce Security Model changes:
- What changed in Salesforce Security Model
- Why change occurred in Salesforce Security Model
- Who approved in Salesforce Security Model
- When implemented in Salesforce Security Model
Auditing Salesforce Security Model
Regular Security Reviews in Salesforce Security Model
Conduct quarterly Salesforce Security Model audits:
- Review user access in Salesforce Security Model
- Verify sharing rules in Salesforce Security Model
- Check for orphaned permissions in Salesforce Security Model
- Validate compliance in Salesforce Security Model
Audit Trail in Salesforce Security Model
Enable audit logging in Salesforce Security Model:
- Setup Audit Trail in Salesforce Security Model
- Track configuration changes in Salesforce Security Model
- Monitor access patterns in Salesforce Security Model
- Detect anomalies in Salesforce Security Model
Testing Salesforce Security Model
Test Before Deployment in Salesforce Security Model
Always test Salesforce Security Model changes:
- Use sandbox for testing in Salesforce Security Model
- Verify all users retain needed access in Salesforce Security Model
- Identify gaps in Salesforce Security Model
- Fix before production in Salesforce Security Model
Common Vulnerabilities in Salesforce Security Model
Understanding vulnerabilities helps prevent Salesforce Security Model weaknesses.
Over-Permissive OWD in Salesforce Security Model
Risk in Salesforce Security Model
Setting OWD to Public Read/Write eliminates need for sharing but creates massive security risk in Salesforce Security Model.
Prevention in Salesforce Security Model
Start with Private OWD in Salesforce Security Model. Open access gradually using sharing rules in Salesforce Security Model.
Neglected Permission Review in Salesforce Security Model
Risk in Salesforce Security Model
Not reviewing permissions in Salesforce Security Model means employees retain access after role changes in Salesforce Security Model.
Prevention in Salesforce Security Model
Quarterly permission audits in Salesforce Security Model ensure access matches current roles in Salesforce Security Model.
Inadequate Field-Level Security in Salesforce Security Model
Risk in Salesforce Security Model
Failing to hide sensitive fields in Salesforce Security Model exposes confidential data in Salesforce Security Model.
Prevention in Salesforce Security Model
Classify data and configure field security in Salesforce Security Model based on sensitivity levels in Salesforce Security Model.
Implementing Salesforce Security Model Effectively
Successful Salesforce Security Model implementation requires planning and execution.
Planning Salesforce Security Model Implementation
Current State Analysis in Salesforce Security Model
Understand existing configuration in Salesforce Security Model:
- Review current settings in Salesforce Security Model
- Identify gaps in Salesforce Security Model
- Document issues in Salesforce Security Model
- Plan improvements in Salesforce Security Model
Requirements Gathering for Salesforce Security Model
Identify organizational needs in Salesforce Security Model:
- User access requirements in Salesforce Security Model
- Data sensitivity levels in Salesforce Security Model
- Compliance requirements in Salesforce Security Model
- Business process needs in Salesforce Security Model
Design Phase of Salesforce Security Model
Architecture Design in Salesforce Security Model
Create comprehensive design in Salesforce Security Model:
- Map role hierarchy in Salesforce Security Model
- Design OWD settings in Salesforce Security Model
- Plan sharing rules in Salesforce Security Model
- Define profiles in Salesforce Security Model
Testing Salesforce Security Model Configuration
User Testing in Salesforce Security Model
Test as each user type in Salesforce Security Model:
- Verify record visibility in Salesforce Security Model
- Confirm field access in Salesforce Security Model
- Check feature availability in Salesforce Security Model
- Validate sharing in Salesforce Security Model
Salesforce Security Model for Different Industries
Different industries have unique Salesforce Security Model requirements.
Financial Services Salesforce Security Model
Requirements in Salesforce Security Model
- Strict data segregation in Salesforce Security Model
- Compliance with regulatory bodies in Salesforce Security Model
- Audit trail requirements in Salesforce Security Model
- Customer confidentiality in Salesforce Security Model
Healthcare Salesforce Security Model
HIPAA Compliance in Salesforce Security Model
- Patient data encryption in Salesforce Security Model
- Access restrictions in Salesforce Security Model
- Audit logging in Salesforce Security Model
- Data segregation in Salesforce Security Model
Government Salesforce Security Model
Compliance Requirements in Salesforce Security Model
- FedRAMP certification in Salesforce Security Model
- Data residency in Salesforce Security Model
- Access controls in Salesforce Security Model
- Audit requirements in Salesforce Security Model
Troubleshooting Salesforce Security Model Issues
Common issues arise when implementing Salesforce Security Model.
Users Cannot Access Needed Records in Salesforce Security Model
Causes in Salesforce Security Model
- OWD too restrictive in Salesforce Security Model
- Missing sharing rules in Salesforce Security Model
- Incorrect role hierarchy in Salesforce Security Model
- Profile restrictions in Salesforce Security Model
Solutions in Salesforce Security Model
- Review OWD in Salesforce Security Model
- Create sharing rules in Salesforce Security Model
- Verify role hierarchy in Salesforce Security Model
- Check profile permissions in Salesforce Security Model
Users See Too Much Data in Salesforce Security Model
Causes in Salesforce Security Model
- OWD too permissive in Salesforce Security Model
- Excessive sharing in Salesforce Security Model
- Over-broad role hierarchy in Salesforce Security Model
Solutions in Salesforce Security Model
- Tighten OWD in Salesforce Security Model
- Review sharing rules in Salesforce Security Model
- Adjust role structure in Salesforce Security Model
Future of Salesforce Security Model
Salesforce Security Model continues evolving to address emerging threats.
AI-Powered Security in Salesforce Security Model
Emerging Capabilities in Salesforce Security Model
- Anomaly detection in Salesforce Security Model
- Behavioral analysis in Salesforce Security Model
- Automated threat response in Salesforce Security Model
- Predictive security in Salesforce Security Model
Enhanced Encryption in Salesforce Security Model
Future Developments in Salesforce Security Model
- Stronger encryption standards in Salesforce Security Model
- Field-level encryption expansion in Salesforce Security Model
- Key management improvements in Salesforce Security Model
External DoFollow Links Included
- Salesforce Official Documentation
- Salesforce Setup and Administration
- Salesforce Security Guide
- Salesforce Trust and Compliance
- GDPR Compliance Information
Quick Summary
Salesforce Security Model is the comprehensive framework protecting your organization's most valuable asset - customer data. Throughout this guide, we've covered all five layers of Salesforce Security Model, from Organization-Wide Defaults through field-level security.


